正在加载图片...
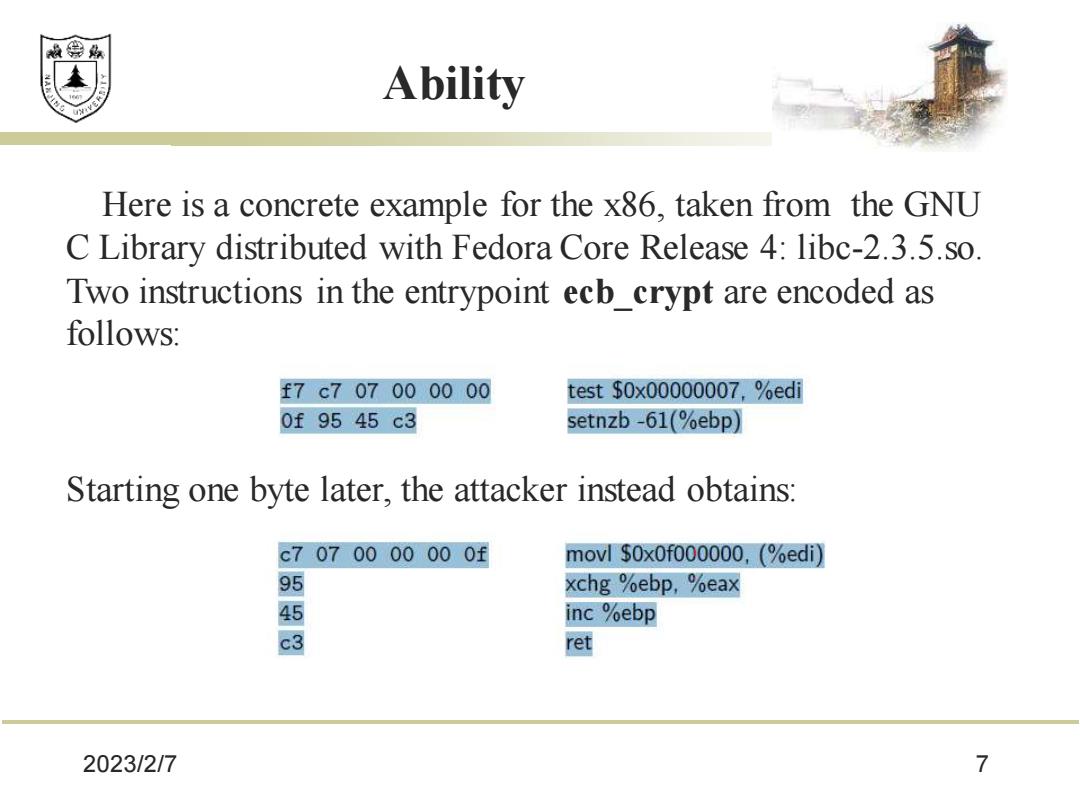
效绵鼎 Abilit女y Here is a concrete example for the x86,taken from the GNU C Library distributed with Fedora Core Release 4:libc-2.3.5.so. Two instructions in the entrypoint ecb_crypt are encoded as follows: f7c707000000 test$0x00000007,%ed 0f9545c3 setnzb-61(%ebp) Starting one byte later,the attacker instead obtains: c7070000000f movl $OxOf000000,(%edi) 9 xchg %ebp,%eax inc %ebp 3 ret 2023/2/7 72023/2/7 7 Ability Here is a concrete example for the x86, taken from the GNU C Library distributed with Fedora Core Release 4: libc-2.3.5.so. Two instructions in the entrypoint ecb_crypt are encoded as follows: Starting one byte later, the attacker instead obtains: