正在加载图片...
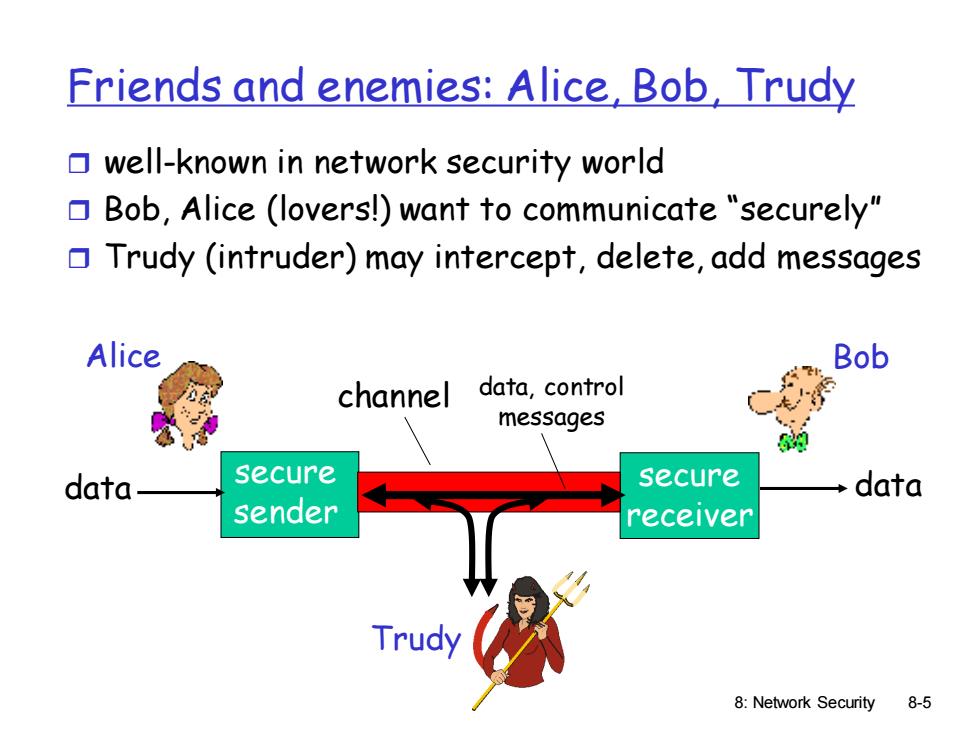
Friends and enemies:Alice,Bob,Trudy well-known in network security world Bob,Alice (lovers!)want to communicate "securely" Trudy (intruder)may intercept,delete,add messages Alice Bob channel data,control messages data secure secure data sender receiver Trudy 8:Network Security 8-5 8: Network Security 8-5 Friends and enemies: Alice, Bob, Trudy well-known in network security world Bob, Alice (lovers!) want to communicate “securely” Trudy (intruder) may intercept, delete, add messages secure sender secure receiver channel data, control messages data data Alice Bob Trudy