正在加载图片...
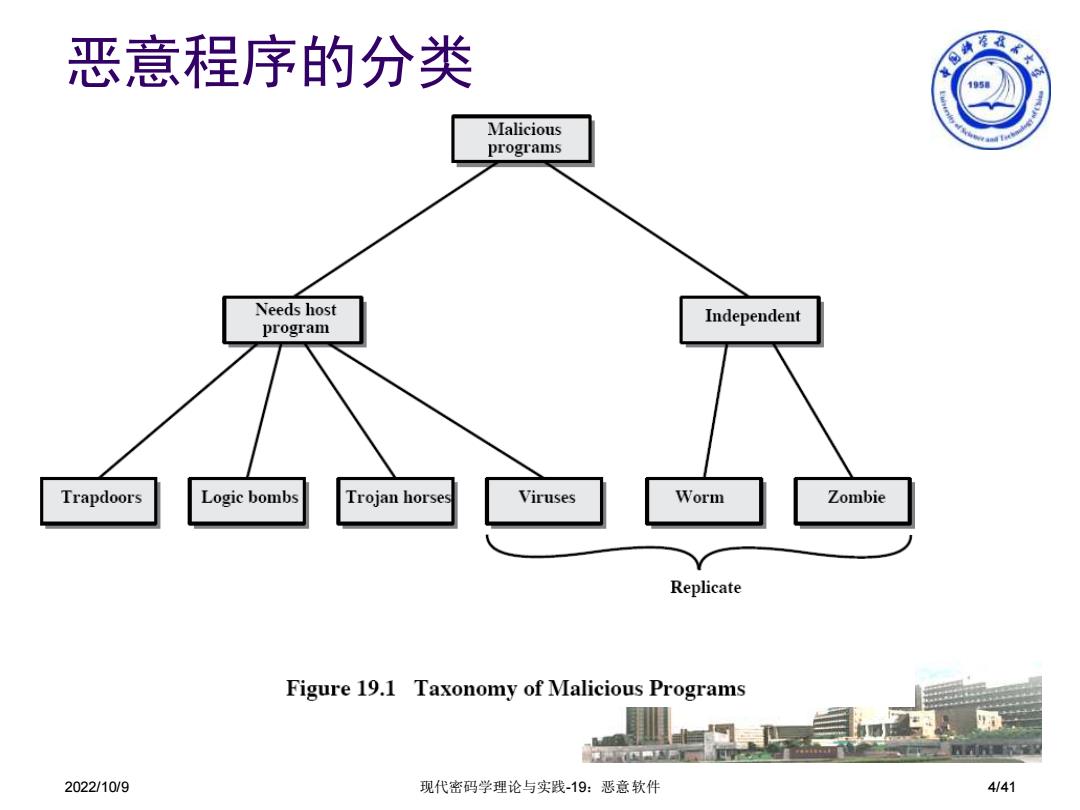
恶意程序的分类 少国海秦家专 1950 Malicious programs Needs host Independent program Trapdoors Logic bombs Trojan horses Viruses Worm Zombie Replicate Figure 19.1 Taxonomy of Malicious Programs 2022/10/9 现代密码学理论与实践-19:恶意软件 4/412022/10/9 现代密码学理论与实践-19:恶意软件 4/41 恶意程序的分类